







Enterprise endpoint protection rollout with centralized management, policy enforcement, threat detection, and automated update governance.
Implementation of data encryption, secure storage, backup alignment, and policy-based access controls to safeguard sensitive information.
Deployment of role-based authentication, multi-factor verification, and directory integration for controlled resource access across systems.
Networked camera setup with secure storage, access permissions, monitoring protocols, and integration with physical security policies.
End-to-end deployment of structured security policies, monitoring systems, incident response workflows, and governance practices across IT environments.

Deployment and rule configuration for perimeter and internal firewalls including traffic filtering, VPN setup, logging, and threat mitigation alignment.
Endpoint protection rollout with centralized management, update automation, threat quarantine, reporting, and compliance enforcement.
Implementation of encryption, secure storage, access restrictions, backup integration, replication, and data integrity validation.

Deployment of identity management, role-based permissions, multi-factor authentication, audit logging, directory integration, and policy governance.
Networked camera deployment with secure access, storage policies, monitoring dashboards, and integration with operational security protocols.
End-to-end execution of security frameworks including monitoring, incident response, vulnerability scanning, policy documentation, and governance enforcement.
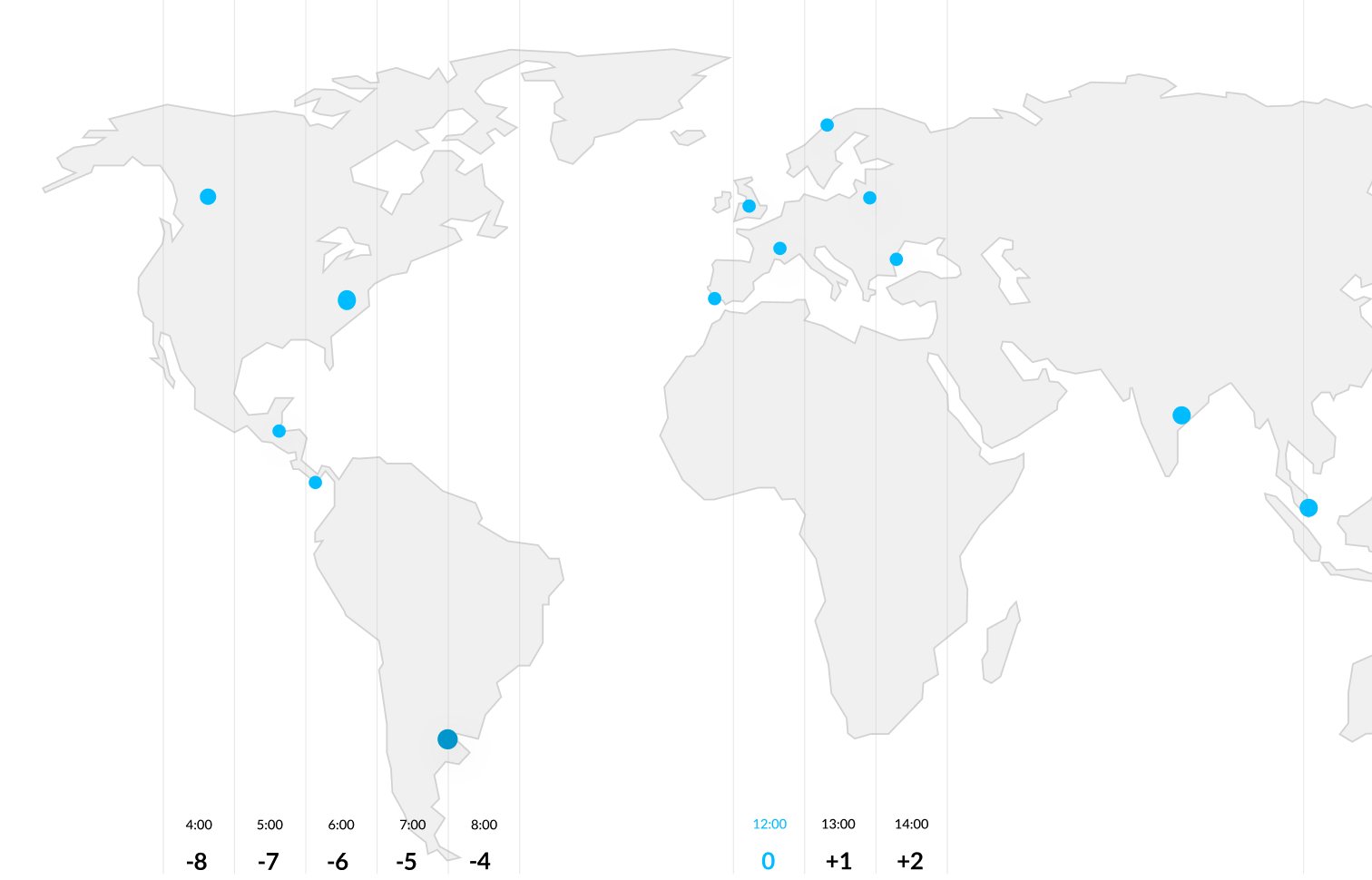
Our industry

Tell us your requirements or questions, and our team will respond quickly with solutions tailored to your business.