







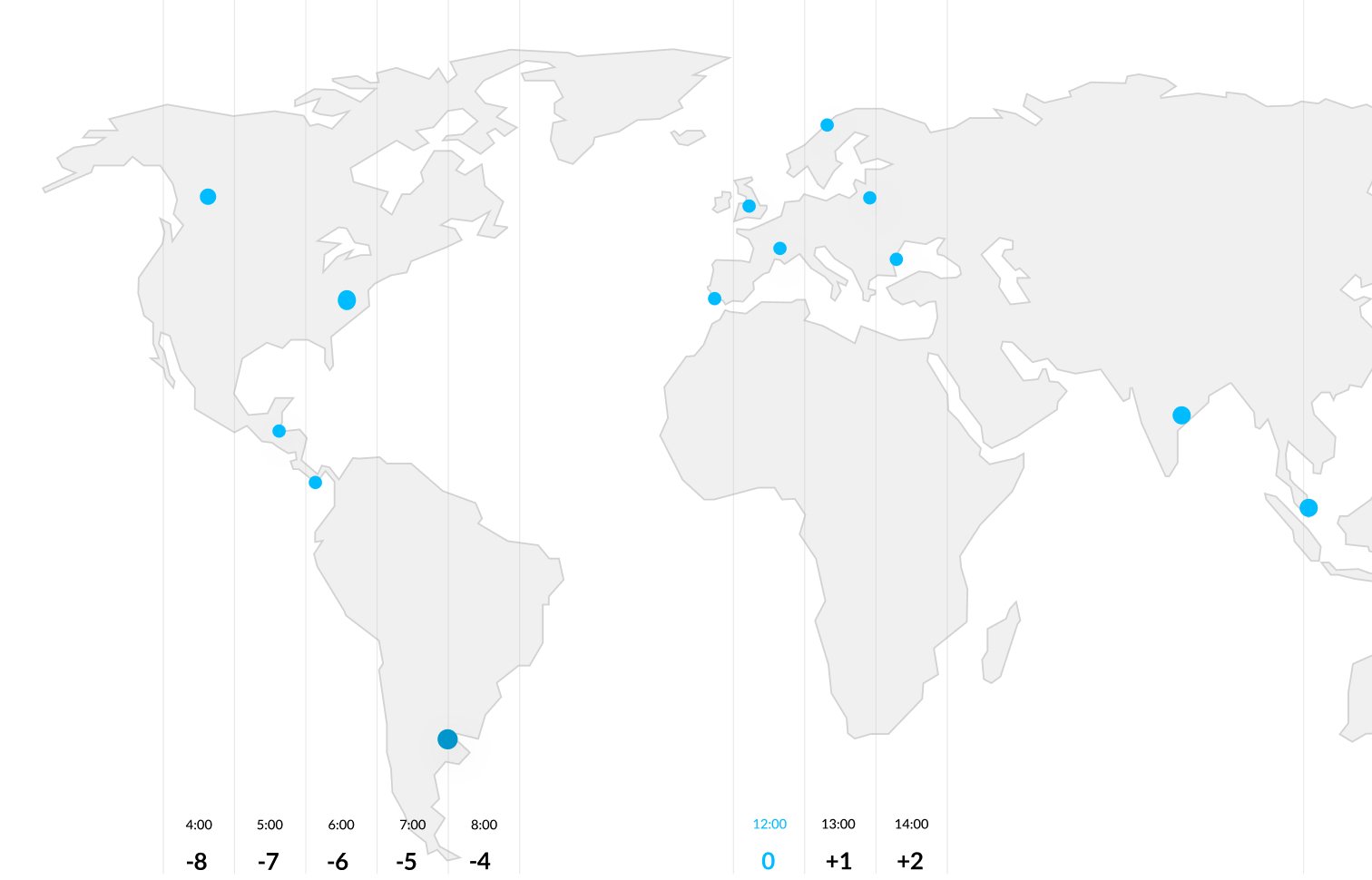
Configuration of network-to-network VPN tunnels enabling secure communication between multiple office locations with redundancy and traffic management.
Implementation of encrypted links, firewall integration, and controlled access policies to safeguard internal communications.
Application of encryption protocols for network traffic, sensitive data, and authentication channels to ensure confidentiality and integrity.

Client VPN installation, authentication setup, traffic encryption, endpoint validation, logging, and integration with directory services.
Configuration of VPN tunnels, routing, redundancy, firewall alignment, traffic optimization, and monitoring.
Deployment of encrypted links, access control, firewall policies, endpoint validation, logging, and monitoring.

Application of encryption for in-transit and at-rest data, key management, protocol enforcement, and compliance alignment.
Our industry

Tell us your requirements or questions, and our team will respond quickly with solutions tailored to your business.